- How will my organization Prepare for cyber threats?
- How will my organization Monitor for cyber threats?
- How will my organization Respond to cyber threats?
- How will my organization Prevent cyber threats?
Back in the days when computers were only seen in episodes of the original Star Trek, cybercrimes were something humans could never possibly imagine.
Companies were more honed into physical crimes—worried about the next Bonnie and Clyde that came to rob their safe. There were also internal threats—employees stealing supplies, money, and written information if they had access.
The same problems still exist, but with the shift to a digital landscape. Cybercrimes are more prevalent and sophisticated than ever.
Therefore, it’s crucial to create a policy to help your organizations avoid or offset cybercrimes’ damage.
Read below for a breakdown of how to put together your cybersecurity policy:
Step #1: Prepare
Preparing a policy and plan to ensure all IT networks and applications are operating with optimal security is integral to successful cybersecurity frameworks. Furthermore, this process can’t disrupt workflow.
More specifically, this policy must outline the assets that need protecting, threats to those assets, and rules/controls to keep the business safe.
Cybersecurity policies are even more vital for businesses with employees (aka most organizations).
Sure, owners and executives would understand the nuts and bolts, likely without any documented mandates. However, employees need an outline that helps them understand their role in protecting tech and data assets.
Your policy should illustrate the following factors to employees:
- The info and data staff are permitted to share.
- Where they can share the data.
- How devices and online materials can be used within workplace parameters.
- Storing and handling sensitive material.
Your policy should also outline matters such as password requirements, email security, social media standards, and incident preparations.
A necessary consideration is how there’s a realistic chance that you could face a cyberattack. As such, your policy must specify the steps you and your team must take when encountering such an incident.
Step #2: Monitoring
With your policy, while you’ll make tweaks and changes to evolve with your business, it’s not continually in motion.
Alternatively, monitoring is ongoing. It centers around ensuring that everyone within your organization upholds the policy’s principles and mandates.
The truth is today’s workplace landscape is increasingly cloud-focused and digitalized in nature. Meaning that there’s a muddying of the traditional network parameters. Yes, preventative securities and tech can mitigate signature-based threats. Unfortunately, without proper monitoring techniques, sophisticated attacks can evade those initial controls.
Monitoring also helps detect cyberattacks while they’re forming and festering, instead of when they’re in full force and can inflict significant damage.
It’s worth mentioning again that monitoring keeps everyone attuned to their behaviors, so they adhere to the policy. Moreover, it detects more threats, helps decrease reaction times to attacks and keeps your company in compliance with regulatory requirements.
There are two different kinds of monitoring tools, both highlighted below:
Network Security Monitoring Tools
- These tools aggregate and analyze security logs from various sources.
- More popular monitoring tool-types are as follows:
- Security Incident and Event Management Systems (SIEM)
- Intrusion Detection (IDS)
- Behavioral Analytics (BA) systems
Endpoint Security Monitoring Tools
- These tools provide transparent security for hosts:
- This gives cybersecurity staff an extra boost to detect threats more proactively, preventing additional damage.
- More popular endpoint tool-types are as follows:
- Endpoint Detection and Response (EDR)
- Endpoint Protection Platforms (EPP)
Step #3: Respond
Monitoring undoubtedly keeps everyone in check and encourages awareness about attacks.
Still, there’s a reason that cybercrimes are projected to cause $6 trillion in damages by 2021. Undoubtedly, a high percentage of that astronomical amount stems from human error and not having a policy or monitoring practices in place.
But many businesses that are stringent with their procedures and tracking get outfoxed by savvy cybercriminals.
These nefarious hackers are evolving and developing increasingly sophisticated techniques that can dupe even the most security-forward company.
Focusing on your company’s response to these threats is something that offsets potential damage.
Think about it like this—when your data is breached, reacting in an ad hoc manner can throw everyone into a frenzy. This kind of chaotic, knee-jerk reaction can exacerbate the problems created. Whereas having a response strategy keeps everything organized and helps companies learn from the experience.
There’s also tremendous value in how a response strategy keeps everyone updated on evolving threats they could potentially face in the future.
To bolster cybercrime response throughout an organization, it’s often wise to partner with a private agency. These companies share data, trends, and risks most relevant to your business, keeping you updated about what to keep an eye on. This helps guide your actions and even adjust your policy.
This way, you can remain reactive to current threats while being prepared for looming future cybersecurity issues.
With all that said, responding is more about pivoting and reacting to the current landscape and unforeseen circumstances. Alternatively, the next step is what’s mostly going to prevent future attacks.
Step #4: Prevent
The ‘Prevent’ facet of your cybersecurity framework focuses on being proactive to stave off future attacks.
In 2020, Artificial Intelligence (AI) is playing a significant role in cyberattack prevention. These technologies thoroughly examine data traffic, information access, transfers, and identify pattern abnormalities through highly proficient algorithms.
When something gets flagged by these AI programs, the technology delves into the data. From there, it’s determined whether there’s been a security breach.
AI also helps prevent cyber threats with the supervised learning method. The algorithms receive both input and output numbers. Over time, they learn how to detect threats and make judgments based on the most frequently seen data.
Supervised learning can perform incredible functions, such as detecting advanced malware disguised as a seemingly innocuous code.
Lastly, it’s worth mentioning that Artificial Intelligence bears a tremendous load, offering business owners and executives immense peace of mind. It streamlines otherwise exhaustive processes while bolstering their long-term functionality.
Conclusion: An Insightful Framework Keeps Your Company Safe from Cybercrimes.
Companies’ various cybersecurity needs will differ depending on their model. However, the framework principles can be similar. With the information provided, you now have an evergreen template to create a successful strategy that prevents and mitigates cyber threats and cybercrimes.
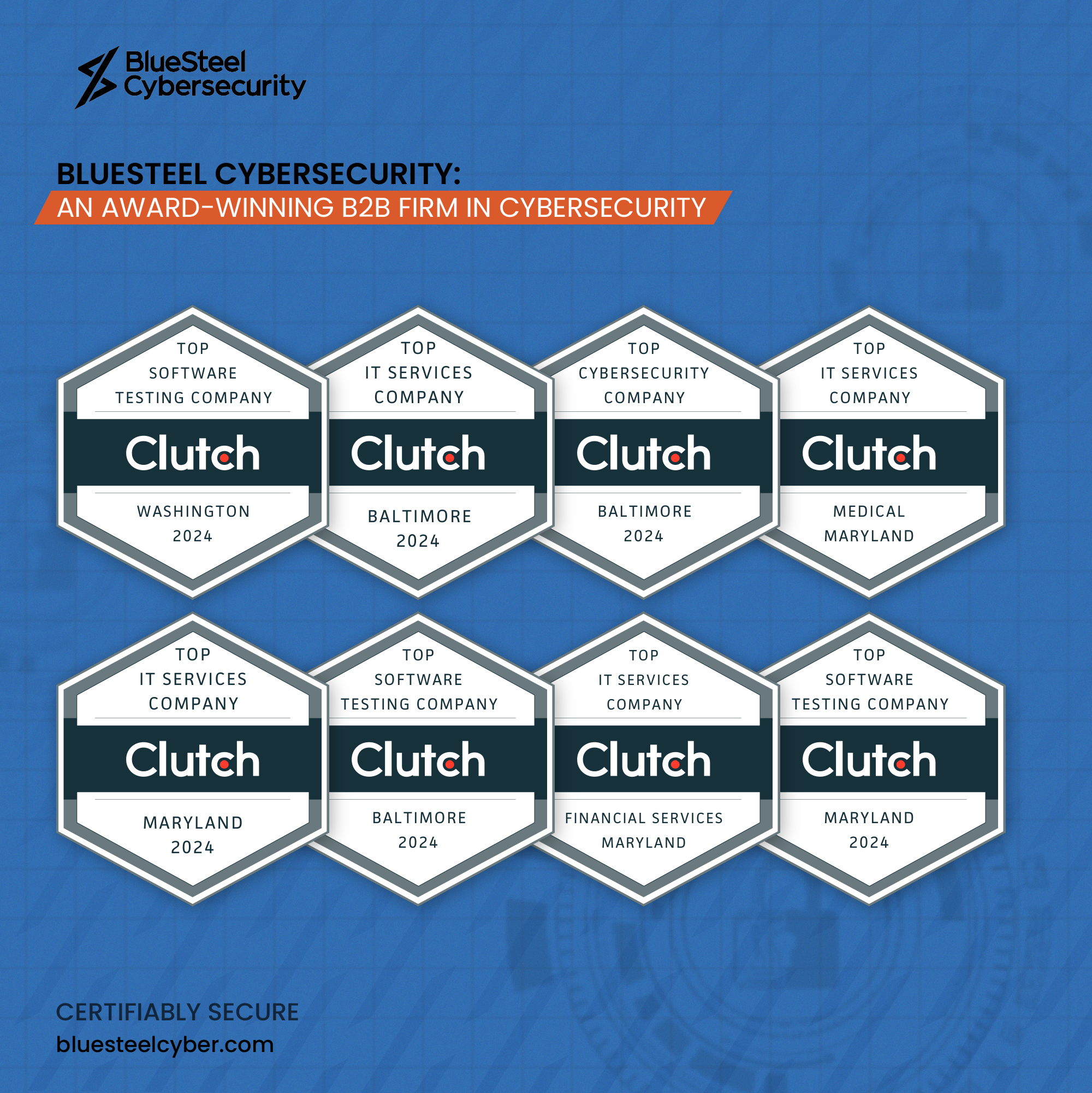
If you need help developing a Cybersecurity Policy that fits your organization, let’s chat today we are one of the best cybersecurity companies in USA